Page 2: Caesar Cipher Project
Unit 4, Lab 2, Page 2
On this page, you will program a shift cipher procedure to encrypt/decrypt text.
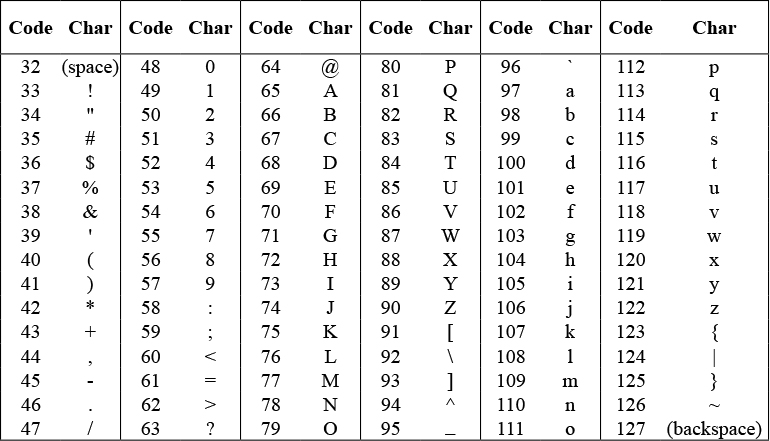
Computers store keyboard characters (capital and small letters, punctuation marks, space, digits, symbols, and so on) as numbers called Unicode. This table shows the Unicode for some of the keyboard characters:
The unicode of block reports the number that is used for a particular character:

The unicode as letter block reports the character that a given Unicode number represents:

-
Experiment with the
unicode ofandunicode as letterblocks. Try changing a word into Unicode, telling the Unicode to a friend, and then having them change it back into a word. - On paper, use a shift cipher to encrypt and decrypt a short message to get a feel for how this cipher works.
- Write a Caesar cipher procedure that works for any input text and any shift value.
- Which character in ciphertext (the coded version) represents a space in the plaintext?
- In this code, 1 becomes 5 and 4 becomes 8, clearly showing the shift of 4. What does 9 become?
- Now test your work. Agree with your partner on a shift value for the encryption. Then use your program to encrypt a secret message and e-mail it to your partner. Then let your partner decrypt your message by using the program to reverse the shift.
Why do we see characters like = ? @ # ^ * { or ~ ?
You can safely assume that shifting any set of text characters a reasonable distance will result in a set of printable characters, which may include non-alphanumeric (not letter or digit) characters.
For example, if we use a shift of 4 to encrypt:
Invasion of Normandy is on 6 June 1944
it becomes:
Mrzewmsr\(sj\)Rsvqerh}\(mw\)sr\(:\)Nyri$5=88
What if your decrypted text is missing some letters?
If you copy your encrypted message with a method other than by using copy and paste (for example, by writing it by hand or typing it into a phone), some characters may disappear from your message. This is because some of the Unicode characters after 126 are printing characters that symbolize things like “delete.” These characters won’t get displayed in Snap!, so you can’t copy them by hand, but if you use copy and paste, Snap! knows they are there. In Take It Further exercise A, you can develop a method of encryption that avoids this problem.
::::::
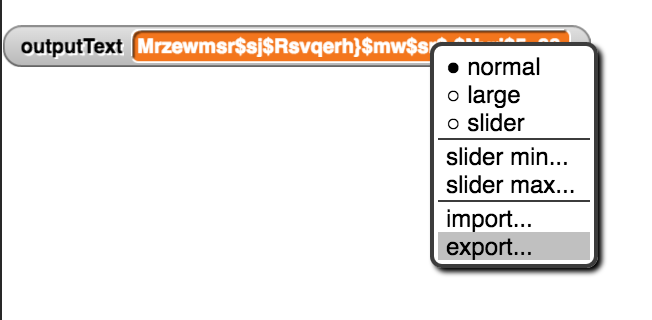
You can extract the encrypted messages from the Snap! interface by right-clicking on the variable that holds the encrypted message and selecting the “Export” option which will download a text file to your computer which then you can copy/paste.
-
Improve your
initialsblock from your U3L2-ContactList project so that it will find the initials for a person with a hyphenated name like Alexandria Ocasio-Cortez.

There are several ways you could solve this problem. Both of the following ways require higher order functions. (You can review the higher order functions
map,keep, andcombineon Unit 3 Lab 2 Page 5: Transforming Every List Item.)-
One way is to use the
unicodeblock to select all the capital letters rather than splitting by word breaks.
-
If you want to use Unicode, you’ll probably want to build or import a block like
is between?from your U2L4-MathLibrary project to check which Unicode values are capital letters. (You learned about exporting and importing blocks on Unit 2 Lab 4 Page 2: Making a Mathematical Library.)
-
If you want to use Unicode, you’ll probably want to build or import a block like
-
Another way is to use the
splitblock to check for hyphens as well as to check for spaces between words.-
If you want to use
split, note that the second input tosplitcan be the character you want to use as the word separator. (You learned aboutspliton Unit 3 Lab 2 Page 5: Transforming Every List Item.)
-
If you want to use
-
- Implement a version of the Caesar Cipher that not only shifts the characters but also wraps them around the alphabet when the end of the alphabet is reached. You may wish to restrict your alphabet to the set of printable characters shown above in the Unicode table.
- Do some research on other types of ciphers used historically. Especially read about the Vigenere Cipher which was used extensively in communicating sensitive information during World War 2.
- Create your own encryption/decryption scheme and implement it in Snap!.